Task
- Directory Brute-forcing is a technique used to check a lot of paths on a web server to find hidden pages. Which is another name for this? (i) Local File Inclusion, (ii) dir busting, (iii) hash cracking.
- dir busting
- What switch do we use for nmap's scan to specify that we want to perform version detection
- -sV
- What does Nmap report is the service identified as running on port 80/tcp?
- http
- What server name and version of service is running on port 80/tcp?
- nginx 1.14.2
- What switch do we use to specify to Gobuster we want to perform dir busting specifically?
- dir
- When using gobuster to dir bust, what switch do we add to make sure it finds PHP pages?
- -x php
- What page is found during our dir busting activities?
- admin.php
- What is the HTTP status code reported by Gobuster for the discovered page?
- 200
Write Up
nmap으로 포트 스캐닝을 해준다.

http 서버가 열려있으니 웹에 접속해보겠다.
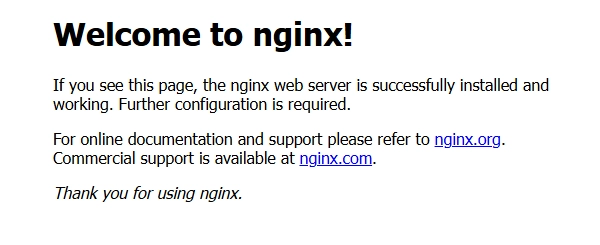
당장 특별한 건 없어서 dir 스캐닝을 해보겠다.
`gobuster dir -u http://10.129.13.239 -w /usr/share/wordlists/SecLists/Discovery/Web-Content/common.txt`

admin.php를 확인해보면 아래와 같이 로그인 화면이 나온다.
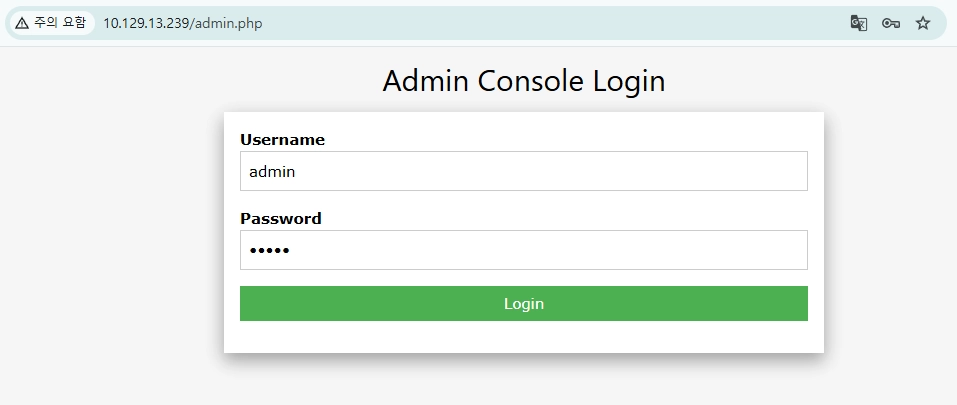
대충 admin admin입력하니 플래그가 나왔다

.
'HackTheBox' 카테고리의 다른 글
| [Tier0] Synced (rsync) (0) | 2026.03.28 |
|---|---|
| [Tier0] Mongod (MongoDB) (0) | 2026.03.28 |
| [Tier0] Explosion (rdp) (0) | 2026.03.28 |
| [Tier0] Redeemer (redis) (1) | 2026.03.27 |
| [Tier0] Dancing (smb) (1) | 2026.03.27 |